Last updated on March 27, 2026
Overview of MFA for SSH on Linux
Supported Systems
* Rublon for SSH is not compatible with SUSE Linux Enterprise Server 11 and 12 due to their outdated versions of GCC. If this is a requirement for you, contact Rublon Support.
Minimum Hardware Requirements:
- 1 CPU core
- 10 MB free disk space
- 10 MB RAM
Note: The connector itself uses only a small amount of CPU and typically consumes tens of kilobytes of memory during operation. The figures above include additional runtime overhead required by the application, shared libraries, and system environment.
Supported Authentication Methods
Demo Video
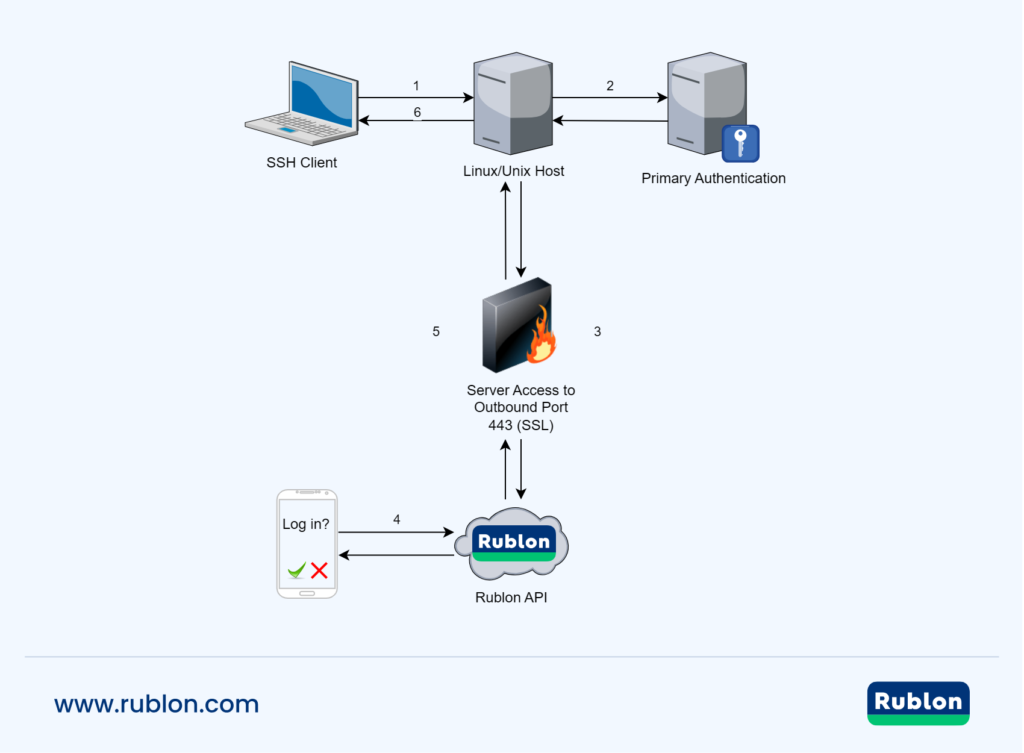
Network Diagram
Known Limitations
Before You Start
Create an Application in the Rublon Admin Console
Install Rublon Authenticator
Installing Rublon MFA for Linux SSH
sudo dpkg -i <package_name>sudo yum install <package_name>sudo zypper install <package_name>Note
Updating the Configuration File
/etc/rublon.configPer-Service Overrides
Since version 2.3.2, the connector can read module arguments (Rublon options) defined directly in PAM service files (for example, /etc/pam.d/sshd, /etc/pam.d/sudo, /etc/pam.d/su).
When present, arguments defined in these files override the corresponding settings from /etc/rublon.config for that specific PAM service only.
This overriding ability lets you keep a global baseline in /etc/rublon.config and apply stricter or different behavior per service (e.g., stronger security on sshd, different UX for sudo).
Example – force non-interactive mode only for SSH:
In /etc/pam.d/sshd, append the Rublon options you want for SSH after the mention of the pam_rublon.so module:
auth sufficient pam_rublon.so nonInteractiveMode=trueSSH logins will use nonInteractiveMode=true, while other services (e.g., sudo, su) will continue to use the value from /etc/rublon.config unless you also override them in their own PAM files. This follows standard Linux-PAM semantics: each file under /etc/pam.d/ is a per-service policy where you can pass module-specific arguments.
Modifying the SUDO Service Configuration
Debian and Ubuntu
@include common-auth#@include common-auth
auth required pam_env.so
auth requisite pam_unix.so
auth sufficient pam_rublon.so
auth required pam_deny.soNote: Starting from version 2.3.2 of the connector, arguments supplied to pam_rublon.so in this file take precedence over the same options in /etc/rublon.config for this service only. Simply append the arguments to be overridden after line auth sufficient pam_rublon.so. More information: Per-Service Overrides.
CentOS and RHEL
auth include system-auth#auth include system-auth
auth required pam_env.so
auth requisite pam_unix.so
auth sufficient pam_rublon.so
auth required pam_deny.soNote: Starting from version 2.3.2 of the connector, arguments supplied to pam_rublon.so in this file take precedence over the same options in /etc/rublon.config for this service only. Simply append the arguments to be overridden after line auth sufficient pam_rublon.so. More information: Per-Service Overrides.
Modifying the SU Service Configuration
Debian and Ubuntu
@include common-auth#@include common-auth
auth required pam_env.so
auth requisite pam_unix.so
auth sufficient pam_rublon.so
auth required pam_deny.soNote: Starting from version 2.3.2 of the connector, arguments supplied to pam_rublon.so in this file take precedence over the same options in /etc/rublon.config for this service only. Simply append the arguments to be overridden after line auth sufficient pam_rublon.so. More information: Per-Service Overrides.
CentOS and RHEL
auth substack system-auth#auth substack system-auth
auth required pam_env.so
auth requisite pam_unix.so
auth sufficient pam_rublon.so
auth required pam_deny.soNote: Starting from version 2.3.2 of the connector, arguments supplied to pam_rublon.so in this file take precedence over the same options in /etc/rublon.config for this service only. Simply append the arguments to be overridden after line auth sufficient pam_rublon.so. More information: Per-Service Overrides.
Enable Rublon MFA for SSH Key Authentication (Optional)
sudo sh /usr/share/rublon/inst_pubkey.shsudo sh /usr/share/rublon/inst_pubkey_rhel_8.shsudo sh /usr/share/rublon/inst_pubkey_rhel_9.shEnable Rublon MFA for Active Directory (Optional)
Rublon MFA for Linux SSH is compatible with systems that authenticate users through Active Directory. This includes systems that use modules such as:
- SSSD (pam_sss.so)
- Winbind (pam_winbind.so)
- Other LDAP or identity provider modules
Rublon MFA does not modify or configure your AD integration. The process of joining the Linux host to the domain and enabling AD authentication is entirely managed by your environment and tools (e.g., realm join, SSSD configuration, or Winbind/Samba configuration)
PAM evaluates authentication modules in the order in which they appear. To ensure the standard MFA behavior, where the password challenge comes first, the module responsible for AD authentication must be placed before “auth sufficient pam_rublon.so” in the PAM auth stack.
This means:
- If your system uses SSSD, ensure that pam_sss.so appears before auth sufficient pam_rublon.so.
- If your system uses Winbind, ensure that pam_winbind.so appears before auth sufficient pam_rublon_mfa.so.
This ensures that:
- The system verifies the user’s identity (via AD) first.
- Rublon MFA is triggered only after successful primary authentication.
- No additional changes to your AD, SSSD, Winbind, or LDAP configuration are required.
We recommend you leave at least one root shell session active and open while making changes to your PAM configuration to prevent accidentally locking yourself out. Additionally, always make sure your PAM configuration works locally before testing it with SSH logins.
Auto Push – Use Case
SCP command example

Updating Rublon MFA for Linux SSH
Uninstalling Rublon MFA for Linux SSH
sudo apt purge rublon-ssh-pamsudo yum remove rublon-sshsudo zypper remove rublon-sshNote
Troubleshooting
Uninstallation and Post-Uninstallation Issues
auth required pam_rublon.so
account required pam_rublon.soKnown Issue with Uninstalling version 2.1.X on RHEL 9

SSH Key Authentication Troubleshooting
UsePAM yes
LoginGraceTime 15m
ChallengeResponseAuthentication yes
AuthenticationMethods publickey,keyboard-interactive
MaxAuthTries 3
PubkeyAuthentication yes
PasswordAuthentication noauth requisite pam_rublon.so
account required pam_rublon.so#@include common-authauth required pam_rublon.so#auth substack password-authservice sshd statussystemctl status sshdGeneral Issues
ChallengeResponseAuthentication yes
UsePAM yes
PasswordAuthentication yesTip