Scalable OpenGroupware.org (SOGo) is an open source webmail for businesses and communities that allows sharing your calendars, address books, and mails in your organization. SOGo offers a dynamic, AJAX-powered web interface and ensures broad compatibility with native clients by leveraging widely adopted protocols like CalDAV, CardDAV, and GroupDAV, along with support for Microsoft ActiveSync.
Multi-Factor Authentication (MFA) for SOGo adds an extra layer of security to SOGo logins. Users must complete both primary (login/password) and secondary (e.g., Mobile Push) authentication. Even if a cybercriminal knows a user’s password, they will not gain access without completing the second step.
Overview of MFA for SOGo
This documentation describes how to integrate Rublon MFA with SOGo using the LDAP(S) protocol to enable multi-factor authentication for logins to the controller.
Rublon MFA for SOGo integrates via the Rublon Authentication Proxy, supporting the LDAP(S) protocol. It ensures that only authorized users can complete the secondary authentication method, denying access to potential intruders.
Supported Authentication Methods
| Authentication Method | Supported | Comments |
| Mobile Push | ✔ | N/A |
| FIDO | – | N/A |
| Passcode | ✔ | N/A |
| SMS Passcode | – | N/A |
| SMS Link | ✔ | N/A |
| Phone Call | ✔ | N/A |
| QR Code | – | N/A |
| Email Link | ✔ | N/A |
| YubiKey OTP | ✔ | N/A |
| RFID | – | N/A |
Before You Start Configuring MFA for SOGo
Before configuring Rublon MFA for SOGo:
- Ensure you have prepared all required components.
- Create an application in the Rublon Admin Console.
- Install the Rublon Authenticator mobile app.
Required Components
1. User Identity Provider (IdP) – You need an external Identity Provider, such as Microsoft Active Directory, OpenLDAP, or FreeIPA.
2. Rublon Authentication Proxy – Install the Rublon Authentication Proxy if you have not already, and configure the Rublon Authentication Proxy as an LDAP proxy.
3. SOGo – A properly installed and configured SOGo server.
Create an Application in the Rublon Admin Console
1. Sign up for the Rublon Admin Console. Here’s how.
2. In the Rublon Admin Console, go to the Applications tab and click Add Application.
3. Enter a name for your application (e.g., SOGo) and then set the type to Rublon Authentication Proxy.
4. Click Save to add the new application in the Rublon Admin Console.
5. Copy the values of System Token and Secret Key of the newly created application. You will need them later.
Install Rublon Authenticator
Some end-users may use the Rublon Authenticator mobile app. So, as a person configuring MFA for SOGo, we highly recommend you install the Rublon Authenticator mobile app, too. Thanks to that, you will be able to test MFA for SOGo via Mobile Push.
Download the Rublon Authenticator for:
Configuring Multi-Factor Authentication (MFA) for SOGo
Rublon Authentication Proxy
1. Edit the Rublon Auth Proxy configuration file and paste the previously copied values of System Token and Secret Key in system_token and secret_key, respectively.
2. Config example file in YAML:
log:
debug: true
rublon:
api_server: https://core.rublon.net
system_token: YOURSYSTEMTOKEN
secret_key: YOURSECRETKEY
proxy_servers:
- name: LDAP-Proxy
type: LDAP
ip: 0.0.0.0
port: 636
auth_source: LDAP_SOURCE_1
auth_method: push, email
rublon_section: rublon
cert_path: /etc/ssl/certs/ca.crt
pkey_path: /etc/ssl/certs/key.pem
auth_sources:
- name: LDAP_SOURCE_1
type: LDAP
ip: 192.0.2.0
port: 636
transport_type: ssl
search_dn: dc=example,dc=org
access_user_dn: cn=admin,dc=example,dc=org
access_user_password: CHANGE_ME
ca_certs_dir_path: /etc/ssl/certs/See: How to set up LDAPS certificates in the Rublon Authentication Proxy?
SOGo
Open the sogo.conf file and add a “SOGoUserSources =” block with the LDAP information. Refer to the following final block and table.
SOGoUserSources = (
{
type = ldap;
CNFieldName = cn;
UIDFieldName = sAMAccountName;
bindFields = (sAMAccountName, userPrincipalName);
baseDN = "ou=Users,dc=my,dc=organization,dc=domain";
bindDN = "CN=rublonadmin,OU=Rublon,DC=rublondemo,DC=local";
bindPassword = "eHJFKF5jC5QqM6ci";
canAuthenticate = YES;
hostname = "ldaps://192.0.2.0:636";
filter = "objectClass='user'";
id = directory;
}
);| type | Set to ldap to define LDAP as the source of user data. |
| CNFieldName | Set to cn to define the Common Name attribute as the field containing the full name of the user. |
| UIDFieldName | Set to sAMAccountName to define this attribute as the user’s unique identifier (login) field. |
| bindFields | Set to (sAMAccountName, userPrincipalName) to allow users to log in using both sAMAccountName and userPrincipalName. |
| baseDN | Enter the Base DN from which SOGo should start searching for users (e.g., “ou=Users,dc=my,dc=organization,dc=domain”). This must match what the bind account “sees”. |
| bindDN | The Bind DN (the full LDAP path of the service account, e.g., “CN=rublonadmin,OU=Rublon,DC=rublondemo,DC=local”) that SOGo will use to authenticate and access the LDAP directory for querying user information.This account must have at least the permission to read other users’ attributes. Note: This Bind DN must be the same as access_user_dn in your Rublon Auth Proxy’s config file. |
| bindPassword | The password of the user defined in bindDN. Note: This Bind password must be the same as access_user_password in your Rublon Auth Proxy’s config file. |
| canAuthenticate | Set to YES to confirm that this data source can be used to authenticate (login) users. |
| hostname | Enter the IP address and port of the Rublon Authentication Proxy, prefixed with ldap:// for LDAP or ldaps:// for LDAPS. LDAPS Example: “ldaps://192.0.2.0:636” LDAP Example: “ldap://192.0.2.0:389” |
| filter | Set to “objectClass=’user’” to limit LDAP searches to only objects that have the class user. |
| id | Set to directory to give a unique “directory” identifier for this user source configuration. |
For more information, refer to the official SOGo LDAP authentication documentation.
Testing Multi-Factor Authentication (MFA) for SOGo
This example portrays logging in to SOGo with Rublon Multi-Factor Authentication. Mobile Push has been set as the second factor in the Rublon Authentication Proxy configuration (AUTH_METHOD was set to push).
1. Open the SOGo panel, enter your login and password, and press Enter.
2. Rublon will send a Mobile Push authentication request to your phone. Tap APPROVE.
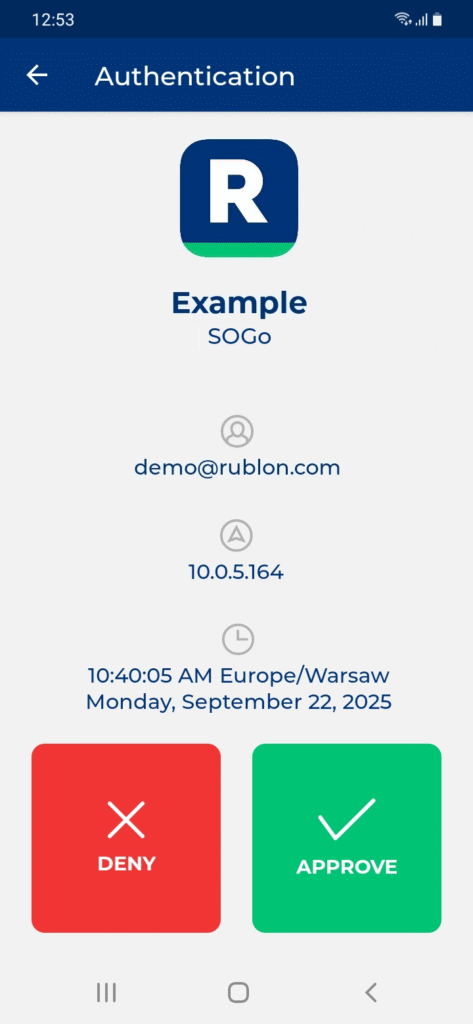
3. You will be logged in to SOGo.
Troubleshooting MFA for SOGo
If you encounter any issues with your Rublon integration, please contact Rublon Support.